Добавить любой RSS - источник (включая журнал LiveJournal) в свою ленту друзей вы можете на странице синдикации.
Исходная информация - http://planet.mozilla.org/.
Данный дневник сформирован из открытого RSS-источника по адресу http://planet.mozilla.org/rss20.xml, и дополняется в соответствии с дополнением данного источника. Он может не соответствовать содержимому оригинальной страницы. Трансляция создана автоматически по запросу читателей этой RSS ленты.
По всем вопросам о работе данного сервиса обращаться со страницы контактной информации.
[Обновить трансляцию]
Cameron Kaiser: TenFourFox not vulnerable to CVE-2019-17026 |
http://tenfourfox.blogspot.com/2020/01/tenfourfox-not-vulnerable-to-cve-2019.html
|
|
The Mozilla Blog: Expanding Mozilla’s Boards in 2020 |
Mozilla is a global community that is building an open and healthy internet. We do so by building products that improve internet life, giving people more privacy, security and control over the experiences they have online. We are also helping to grow the movement of people and organizations around the world committed to making the digital world healthier.
As we grow our ambitions for this work, we are seeking new members for the Mozilla Foundation Board of Directors. The Foundation’s programs focus on the movement building side of our work and complement the products and technology developed by Mozilla Corporation.
What is the role of a Mozilla board member?
I’ve written in the past about the role of the Board of Directors at Mozilla.
At Mozilla, our board members join more than just a board, they join the greater team and the whole movement for internet health. We invite our board members to build relationships with management, employees and volunteers. The conventional thinking is that these types of relationships make it hard for the Executive Director to do his or her job. I wrote in my previous post that “We feel differently”. This is still true today. We have open flows of information in multiple channels. Part of building the world we want is to have built transparency and shared understandings.
It’s worth noting that Mozilla is an unusual organization. We’re a technology powerhouse with broad internet openness and empowerment at its core. We feel like a product organization to those from the nonprofit world; we feel like a non-profit organization to those from the technology industry.
It’s important that our board members understand the full breadth of Mozilla’s mission. It’s important that Mozilla Foundation Board members understand why we build consumer products, why it happens in the subsidiary and why they cannot micro-manage this work. It is equally important that Mozilla Corporation Board members understand why we engage in the open internet activities of the Mozilla Foundation and why we seek to develop complementary programs and shared goals.
What are we looking for?
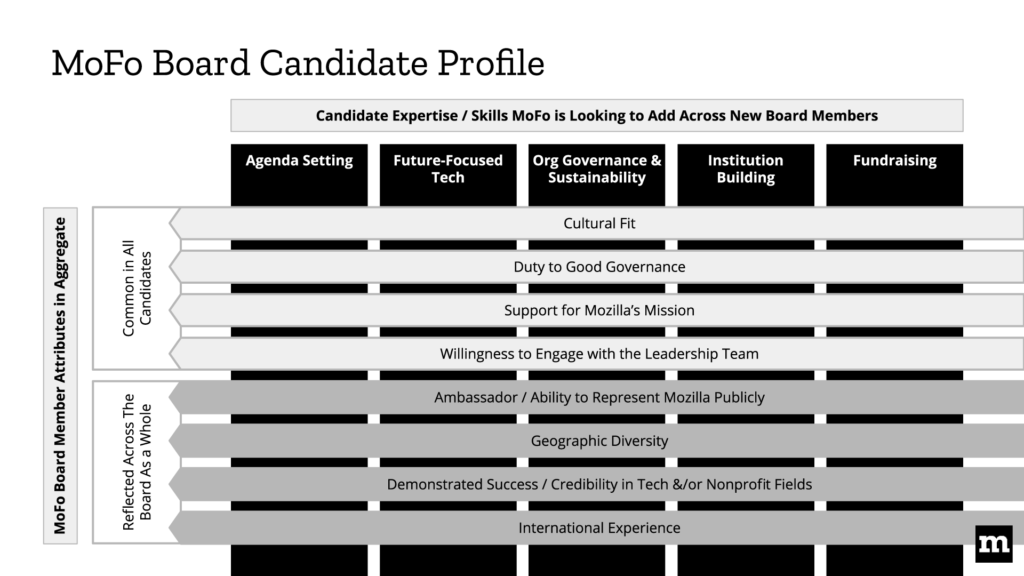
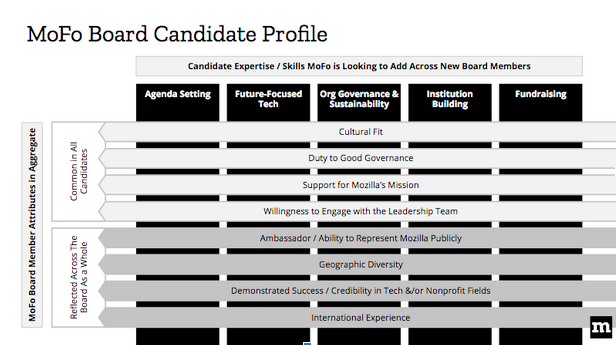
Last time we opened our call for board members, we created a visual role description. Below is an updated version reflecting the current needs for our Mozilla Foundation Board.
Here is the full job description: https://mzl.la/MoFoBoardJD
Here is a short explanation of how to read this visual:
- In the vertical columns, we have the particular skills and expertise that we are looking for right now. We expect new board members to have at least one of these skills.
- The horizontal lines speaks to things that every board member should have. For instance, to be a board member, you should have to have some cultural sense of Mozilla. They are a set of things that are important for every candidate. In addition, there is a set of things that are important for the board as a whole. For instance, international experience. The board makeup overall should cover these areas.
- The horizontal lines will not change too much over time, whereas the vertical lines will change, depending on who joins the Board and who leaves.
Finding the right people who match these criteria and who have the skills we need takes time. We hope to have extensive discussions with a wide range of people. Board candidates will meet the existing board members, members of the management team, individual contributors and volunteers. We see this as a good way to get to know how someone thinks and works within the framework of the Mozilla mission. It also helps us feel comfortable including someone at this senior level of stewardship.
We want your suggestions
We are hoping to add three new members to the Mozilla Foundation Board of Directors over the next 18 months. If you have candidates that you believe would be good board members, send them to msurman@mozillafoundation.org. We will use real discretion with the names you send us.
The post Expanding Mozilla’s Boards in 2020 appeared first on The Mozilla Blog.
https://blog.mozilla.org/blog/2020/01/08/expanding-mozillas-boards-in-2020/
|
|
Mitchell Baker: Expanding Mozilla’s Boards in 2020 |
Mozilla is a global community that is building an open and healthy internet. We do so by building products that improve internet life, giving people more privacy, security and control over the experiences they have online. We are also helping to grow the movement of people and organizations around the world committed to making the digital world healthier.
As we grow our ambitions for this work, we are seeking new members for the Mozilla Foundation Board of Directors. The Foundation’s programs focus on the movement building side of our work and complement the products and technology developed by Mozilla Corporation.
What is the role of a Mozilla board member?
I’ve written in the past about the role of the Board of Directors at Mozilla.
At Mozilla, our board members join more than just a board, they join the greater team and the whole movement for internet health. We invite our board members to build relationships with management, employees and volunteers. The conventional thinking is that these types of relationships make it hard for the Executive Director to do his or her job. I wrote in my previous post that “We feel differently”. This is still true today. We have open flows of information in multiple channels. Part of building the world we want is to have built transparency and shared understandings.
It’s worth noting that Mozilla is an unusual organization. We’re a technology powerhouse with broad internet openness and empowerment at its core. We feel like a product organization to those from the nonprofit world; we feel like a non-profit organization to those from the technology industry.
It’s important that our board members understand the full breadth of Mozilla’s mission. It’s important that Mozilla Foundation Board members understand why we build consumer products, why it happens in the subsidiary and why they cannot micro-manage this work. It is equally important that Mozilla Corporation Board members understand why we engage in the open internet activities of the Mozilla Foundation and why we seek to develop complementary programs and shared goals.
What are we looking for?
Last time we opened our call for board members, we created a visual role description. Below is an updated version reflecting the current needs for our Mozilla Foundation Board.
Here is the full job description: https://mzl.la/MoFoBoardJD
Here is a short explanation of how to read this visual:
- In the vertical columns, we have the particular skills and expertise that we are looking for right now. We expect new board members to have at least one of these skills.
- The horizontal lines speaks to things that every board member should have. For instance, to be a board member, you should have to have some cultural sense of Mozilla. They are a set of things that are important for every candidate. In addition, there is a set of things that are important for the board as a whole. For instance, international experience. The board makeup overall should cover these areas.
- The horizontal lines will not change too much over time, whereas the vertical lines will change, depending on who joins the Board and who leaves.
Finding the right people who match these criteria and who have the skills we need takes time. We hope to have extensive discussions with a wide range of people. Board candidates will meet the existing board members, members of the management team, individual contributors and volunteers. We see this as a good way to get to know how someone thinks and works within the framework of the Mozilla mission. It also helps us feel comfortable including someone at this senior level of stewardship.
We want your suggestions
We are hoping to add three new members to the Mozilla Foundation Board of Directors over the next 18 months. If you have candidates that you believe would be good board members, send them to msurman@mozillafoundation.org. We will use real discretion with the names you send us.
https://blog.lizardwrangler.com/2020/01/08/expanding-mozillas-boards-in-2020/
|
|
Wladimir Palant: Avast complies to respect users' privacy |
December last year has been an interesting month in Avast-land. After my investigation into Avast’s data collection practices didn’t attract any attention initially, Mozilla and Opera removed Avast’s browser extensions from their respective add-on stores immediately after I reported them. Google spent two weeks evaluating the issue but eventually did the same. The matter of Avast selling users’ data even attracted attention of high-level politicians.

Avast’s official communication throughout that month was nothing short of amazing. I found it hard to believe that a company could keep denying any wrongdoing despite all the evidence to the contrary. Avast’s CEO Ondrej Vlcek even gave an interview to the Forbes magazine where he claimed that there was no privacy scandal here. Users clearly disagreed, and so did most journalists. But the company’s stance didn’t change: all the data collected is necessary to protect users, and selling it later without user’s agreement is completely unproblematic due to the data being “anonymized.”
So when on December 22nd they finally brought out updated versions of their extensions, I was very curious to see what they changed other than writing a usable privacy policy. The updates have been accepted by all browser vendors and, at the time of writing, all four extensions are available for Firefox and Chrome. The Opera Add-ons site currently lists three extensions, with Avast Online Security still missing.
Let’s say this much up front: the changes are far more extensive and far more convincing than I would have expected. While Chrome and Opera versions appear identical however, there are some additional changes in the Firefox version. That’s presumably to comply with stricter privacy requirements of the Mozilla Add-ons site.
Update (2020-01-10): Avast contacted me to clarify the situation. One piece of information stood out here: “we completely discontinued the practice of using any data from the browser extensions for any other purpose than the core security engine.” In other words, Avast isn’t merely doing the bare minimum required to comply with store policies, they completely give up collecting too much data via their browser extensions and they won’t share this data with anybody either. That’s a massive privacy improvement for any Avast users out there. The open question is whether this policy change also applies to the Avast SafePrice extension and Avast Secure Browser. I’ll update the post again once I have the answer. Update (2020-01-11): The quoted statement from Avast seemed unambiguous, yet from further communication it now looks like their plan is to establish sharing data with Jumpshot as opt-in functionality of the free antivirus application. I hope for further clarification about which one it is in the end.
Just to be clear: with the large codebases and without any official information from Avast I might have overlooked some of the changes. On Firefox I looked at Avast Online Security 19.4.426, on Chrome at Avast Online Security 19.4.433 and on Opera at AVG Online Security 19.4.433.
The bogus consent screen
One change is very obvious when you install the Firefox extension. Upon installation the extension will open this consent screen:
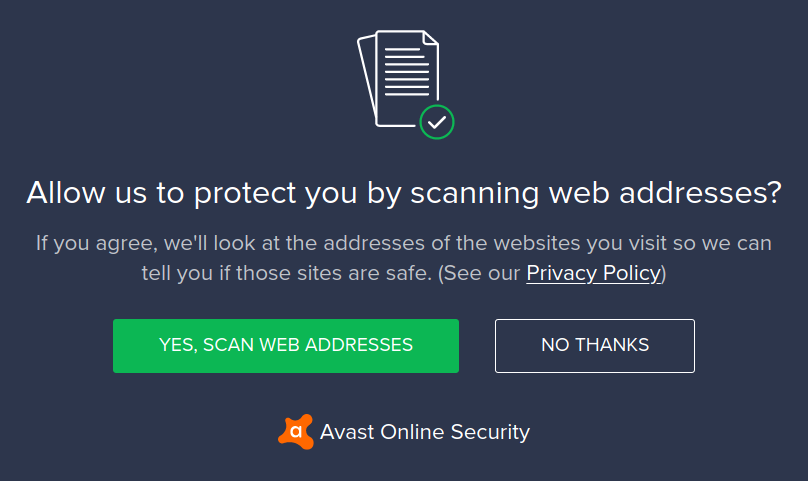
Currently, this only happens if you install Avast Online Security from Mozilla Add-ons website. That’s because the antivirus application installs an older version of the extension, and the consent screen isn’t displayed on updates. I assume however that installs via the antivirus application will also produce this consent screen once a new version of the application is available. Chrome and Opera extensions generally won’t show this screen.
But that doesn’t really matter. Do you think that clicking “No thanks” here will switch the extension to a privacy friendly mode? No, the extension will rather drop dead and suggest that the user uninstalls it. This consent screen satisfies Mozilla’s requirement to have any URL collection be strictly opt-in but the user does not really having a choice here. Luckily, this isn’t the only change.
The “share data with Jumpshot” setting
Update (2020-01-10): This section originally discussed an “Allow usage data to be shared with Jumpshot with analytics” setting only visible to Firefox users. As mentioned above, Avast no longer wants to share extension data with Jumpshot or other third parties. According to them, having this setting still present in the Firefox extension was an oversight and has been corrected in Avast Online Security 19.4.434.
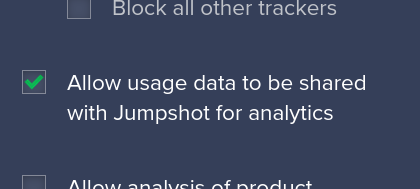
In previous versions this setting was called “Allow usage data to be shared with 3rd parties for analytics.” When analyzing the extension before I didn’t really understand what this setting was doing, because changing it showed so little effect and because of the misleading internal name communityIQ. As I realize now, this setting (and the setting of the same name in the antivirus application) was responsible for the fact that I didn’t see user identifiers being sent to the servers under some conditions.
This setting still exists internally in the current version of the extension. It is off by default however and will only be switched on if the Avast antivirus application is installed and data sharing is allowed there.
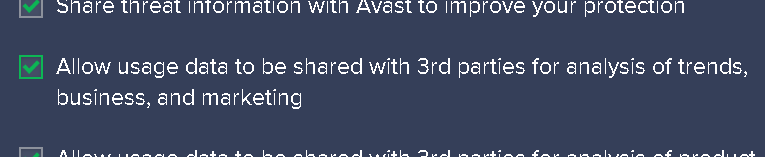
Since the settings of the Avast antivirus application are quite extensive: this particular setting can be found under General > Personal Privacy.
The new data collection practices
If you are a Firefox user, things are quite simple: only minimal data will be sent to Avast now. In addition to the full page address, that data includes information about the extension and the browser you are using.
It’s the same with Chrome and Opera users who didn’t agree to share data with third parties, only a minimal amount of data is sent. If they accepted to share their data however, the extension will send the same data set as previous versions to the Avast servers.
This is a considerable improvement to the previous versions where the “share data” setting had a very limited effect. When unchecked it would ensure that user identifiers are omitted, but otherwise all data would be sent along with a dnl flag (short for “do not log”). Also, this setting was on by default, particularly for users who never installed the antivirus application and hence couldn’t deny data collection on its consent screen.
Update (2020-01-10): Regardless of the browser used, the latest extension versions will now always set the dnl flag. That’s different from Avast Online Security 19.4.426 for Firefox that I looked at two days ago. According to Avast, this flag no longer serves a purpose and will go away eventually.
What does the “dnl” flag do?
Since the dnl flag is being processed on the server side, we can only speculate about what it does. It would be logical to assume that it is being processed according to its name: if data comes in with a request that has the dnl flag set, that data is only used to produce a response but nothing is stored. Given that previous versions of Avast extensions were setting this flag as well and at least users of the Avast antivirus application have seen a consent screen asking them to allow data usage, it would make the whole issue a much smaller one.
There are some oddities here however which make me doubt whether the logical assumption is the correct one. First are the official statements by Avast in reaction to this issue being raised. If data was being shared with Jumpshot only for the users who agreed to it, why not say so? Even if the users have no way to validate this claim, it’s still a much stronger statement than “the data is anonymized, nothing to be concerned about.”
And if the dnl flag is being considered correctly by the server, why is it always set for Chrome and Opera users? With the majority of Avast users on Chrome, I don’t think that Avast would give up so much data intentionally. So it must be a bug, one that has been in production for more than two weeks now. Even with the holiday season, somebody certainly would have noticed a sharp decline in the number of data samples collected? With data being so important to Avast’s business, they certainly would have rushed a fix?
Update (2020-01-10): The speculation in the paragraph above is incorrect, the dnl flag always being set is intentional and not a bug. That’s in line with Avast’s decision to stop sharing data with third parties. So I am now more inclined to believe that historically the dnl flag indeed caused data to be discarded at some point, ideally before this data was passed on to Jumpshot.
And the shopping helpers?
I didn’t spend too much time investigating Avast SafePrice. This extension being a shopping helper, it apparently cannot be expected to be too privacy-friendly. So there is no “data sharing” setting and no dnl flag here. Merely a bogus consent screen was added on Firefox: “either you allow us to collect all this data or the extension won’t be usable.” To add insult to injury, the extension won’t remember you declining or closing this consent screen, so when you restart your browser it will simply assume consent.
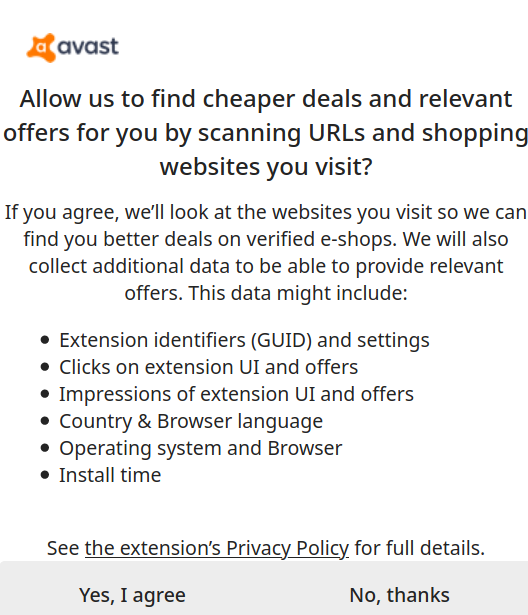
At least I noticed one change to the data collection practices. While the data collected here is still quite extensive and will always contain a unique user identifier as well as window and tab identifiers for example, the page address is now being shortened to contain protocol and host name only. At least that much.
Update (2020-01-10): I clarified that the consent screen is required by Mozilla’s policies. There has been a number of other corrections based on information provided by Avast, these are marked separately.
https://palant.de/2020/01/08/avast-complies-to-respect-users-privacy/
|
|
Daniel Stenberg: curl 7.68.0 with etags and BearSSL |
The year is still young, and we’re here to really kick off 2020 with a brand new curl release! curl 7.68.0 is available at curl.haxx.se as always. Once again we’ve worked hard and pushed through another release cycle to bring you the very best we could do in the 63 days since 7.67.0.
(The previous release was said to be the 186th, but it turned out we’ve been off-by-one on the release counter for a while.)
Numbers
the 188th release
6 changes
63 days (total: 7,964)
124 bug fixes (total: 5,788)
193 commits (total: 25,124)
1 new public libcurl function (total: 82)
0 new curl_easy_setopt() option (total: 269)
3 new curl command line option (total: 229)
70 contributors, 32 new (total: 2,088)
31 authors, 13 new (total: 756)
1 security fixes (total: 93)
400 USD paid in Bug Bounties
Security Vulnerability
CVE-2019-15601: SMB access smuggling via FILE URL on Windows.
Simply put: you could provide a FILE:// URL to curl that could trick it to try to access a host name over SMB – on Windows machines. This could happen because Windows apparently always do this automatically if given the correct file name and curl had no specific filter to avoid it.
For this discovery and report, the curl Bug Bounty program has rewarded Fernando Mu~noz 400 USD.
Changes
We ship a new TLS backend: BearSSL. The 14th.
We ship two new command line options for ETags.
We provide a new API call to wakeup “sleeping” libcurl poll calls.
We changed the default handling in libcurl with OpenSSL for verifying certificates. We now allow “partial chains” by default, meaning that you can use an intermediate cert to verify the server cert, not necessarily the whole chain to the root, like you did before. This brings the OpenSSL backend to work more similar to the other TLS backends, and we offer a new option for applications to switch back on the old behavior (CURLSSLOPT_NO_PARTIALCHAIN).
The progress callback has a new feature: if you return CURL_PROGRESSFUNC_CONTINUE from the callback, it will continue and call the internal progress meter.
The new command line option --parallel-immediate is added, and if used will make curl do parallel transfers like before 7.68.0. Starting with 7.68.0, curl will default to defer new connections and rather try to multiplex new transfer over an existing connection if more than one transfer is specified to be done from the same host name.
Bug-fixes
Some of my favorite fixes done since the last release include…
Azure CI and torture
This cycle we started running a bunch of CI tests on Azure Pipelines, both Linux and macOS tests. We also managed to get torture tests running thanks to the new shallow mode.
Azure seem to run faster and more reliable than Travis CI, so moving a few jobs over has made a total build run often complete in less total time now.
prefer multiplexing to using new connections
A regression was found that made the connection reuse logic in libcurl to prefer new connections to multiplexing more than what was actually intended and once fixed we should see libcurl-using application do more and better HTTP/2 multiplexing.
support for ECDSA and ed25519 knownhost keys with libssh2
libssh2 is the primary SSH backend people use with curl. While the library itself has supported these new “knownhost” keys for a while, we hadn’t previously adjusted curl to play nicely with them. Until now.
openssl: Revert to less sensitivity for SYSCALL errors
Another regression in the OpenSSL backend code made curl overly sensitive to some totally benign TLS messages which would cause a curl error when they should just have been silently handled and closed the connection cleanly.
openssl: set X509_V_FLAG_PARTIAL_CHAIN by default
The OpenSSL backend now behaves more similar to other TLS backends in curl and now accepts “partial” certificate chains. That means you don’t need to have the entire chain locally all the way to the root in order to verify a server certificate. Unless you set CURLSSLOPT_NO_PARTIALCHAIN to enforce that behavior.
parsedate: offer a getdate_capped() alternative
The date parser was extended to make curl handle dates beyond 2038 better on 32 bit systems, which primarily seems to happen with cookies. Now the parser understands that they’re too big and will use the max time value it can hold instead of failing and using a zero, as that would make the cookies into “session cookies” which would have slightly different behavior.
Video presenting the release
https://daniel.haxx.se/blog/2020/01/08/curl-7-68-0-with-etags-and-bearssl/
|
|
Cameron Kaiser: The new Overbite Android (works with Firefox Android too): Gopherspace on your mobile Android device |
Naturally Overbite Android works just fine as a standalone application and responds to any gopher:// intent sent by any other activity, including Firefox. However, this latest version has been updated specially for Android Q support, including dark theme:
I also purged a lot of the old API usage, replacing it with a more Material Design-style UI, an actual address bar you can edit for a change, and a dynamic menu off a floating action button (as opposed to the old school Menu button menu, support for which was removed from Android Q). There are also fixes to scrolling and zooming, and you can still generate and drop shortcuts on your Android launcher as bookmarks.
Now that I've gotten off my butt and converted it to Android Studio, I suppose I should start working on download support again but everything else (including searches) functions just dandy.
Overbite Android is offered to you under the BSD license and supports 4.0 (Ice Cream Sandwich) through 10 (Q). You can get it, the Android Studio project and source code, and all the rest of the Overbite gopher client family from the Overbite website or directly from Gopherspace.
http://tenfourfox.blogspot.com/2020/01/the-new-overbite-android-works-with.html
|
|
Will Kahn-Greene: How to pick up a project with an audit |
Over the last year, I was handed a bunch of projects in various states. One of the first things I do when getting a new project that I'm suddenly responsible for is to audit the project. That helps me figure out what I'm looking at and what I need to do with it next.
This blog post covers my process for auditing projects I'm suddenly the proud owner of.
Read more… (5 min remaining to read)
https://bluesock.org/~willkg/blog/dev/auditing_projects.html
|
|
Given the Indian government’s impending commitment to the Supreme Court to notify the intermediary liability amendments by January 15 2020, global internet organizations Mozilla, GitHub, and Cloudflare have penned an open letter to the Union Minister of Electronics & Information Technology, Shri. Ravi Shankar Prasad. The letter highlights significant concerns with the rules and calls for improved transparency by allowing the public an opportunity to see a final version of these amendments prior to their enactment.
An excerpt from the letter is extracted below, and the full letter is available online:
“On behalf of a group of global internet organisations with millions of users in India, we are writing to urge you to ensure the planned amendments to India’s intermediary liability regime allow for the Internet to remain an open, competitive, and empowering space for Indians. We understand and respect the need to ensure the internet is a safe space where large platforms take appropriate responsibility. However, the last version of these amendments which were available in the public domain suggest that the rules will promote automated censorship, tilt the playing field in favour of large players, substantially increase surveillance, and prompt a fragmentation of the internet in India that would harm users while failing to empower Indians.
The current safe harbour liability protections have been fundamental to the growth of the internet in India. They have enabled hosting platforms to innovate and flourish without fear that they would be crushed by a failure to police every action of their users. Imposing the obligations proposed in these new rules would place a tremendous, and in many cases fatal, burden on many online intermediaries – especially new organizations and companies. A new community or a startup would be significantly challenged by the need to build expensive filtering infrastructure and hire an army of lawyers.
Given your government’s commitment to the Supreme Court of India to notify these rules by January 15, 2020, it is vital that the public has the opportunity to see a final version of these amendments to help ensure that they assuage the concerns which have been voiced by a wide variety of stakeholders during the public consultation. We appeal for this increased transparency and we remain committed to working with you to achieve the broader objective of these amendments while allowing Indians to benefit from a global internet.”
About Mozilla
Mozilla is the not-for-profit behind the popular web browser, Firefox. We believe the Internet is a global public resource, open and accessible to all. We work to ensure it stays open by building products, technologies and programs that put people in control of their online lives, and contribute to a healthier internet. Mozilla is also leading a public petition to Shri. Ravi Shankar Prasad, India’s IT Minister, to make the latest draft of the intermediary liability amendments public prior to their enactment.
About GitHub
GitHub is the developer company. We make it easier for developers to be developers: to work together, to solve challenging problems, to create the world’s most important technologies. We foster a collaborative community that can come together—as individuals and in teams—to create the future of software and make a difference in the world.
About Cloudflare
Cloudflare, Inc. (NYSE: NET / www.cloudflare.com / @cloudflare) is on a mission to help build a better Internet. Cloudflare’s platform protects and accelerates any Internet application online without adding hardware, installing software, or changing a line of code. Internet properties powered by Cloudflare have all web traffic routed through its intelligent global network, which gets smarter with every request. As a result, they see significant improvement in performance and a decrease in spam and other attacks.
The post Open Letter to Indian IT Minister by Mozilla, GitHub, and Cloudflare: Release draft intermediary liability rules, assuage concerns voiced during public consultation appeared first on Open Policy & Advocacy.
|
|
Hacks.Mozilla.Org: Firefox 72 — our first song of 2020 |
2020 is upon us, folks. We’d like to wish everyone reading this a happy new year, wherever you are. As you take your first steps of the new year, figuring out what your next move is, you may find it comforting to know that there’s a new Firefox release to try out!
Version 72 to be exact.
One of the highlights that we are most proud of is that user gestures are now required for a number of permission-reliant methods, such as Notification.requestPermission(). User research commonly brings up permission prompt spam as a top user annoyance, so we decided to do something about it. This change reduces permission spam and strengthens users’ agency over their online experience.
This release brings several other new features, including DevTool improvements such as Watchpoints, WebSockets inspector improvements, and resource download times; support for CSS features like shadow parts, motion path, and transform properties; and JS/API features such as event-based form participation and the nullish coalescing operator.
Read on for more highlights. To find the full list of additions, check out the following MDN articles:
Now that we’ve moved to a 4-week browser release cycle, you’ll see fewer new features in each individual release, but features will be added to Firefox more often. This gives you faster access to new functionality and bug fixes. You can read our full rationale for the change in Moving Firefox to a faster 4-week release cycle.
DevTools improvements
First, we’ll look at Firefox 72 DevTools improvements in more detail.
Pause on variable access or change
Watchpoints are a new type of breakpoint that can pause execution when an object property gets read or set. You can set watchpoints from the context menu of any object listed in the Scopes panel.
This feature is described in more detail in the Use watchpoints article on MDN, and Debugging Variables With Watchpoints in Firefox 72 on Hacks.
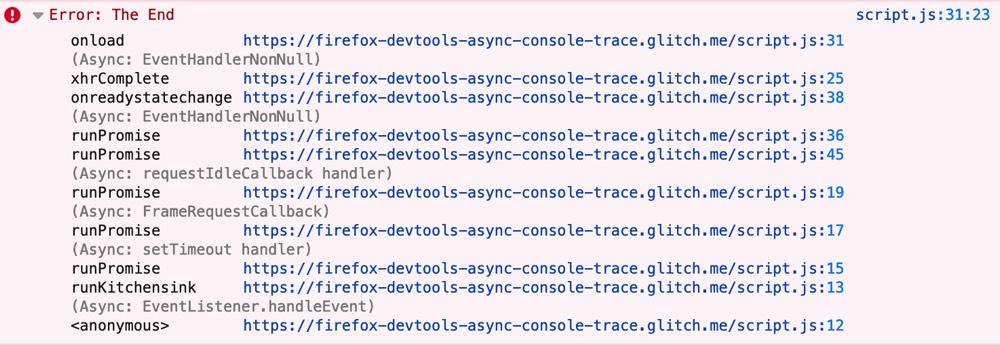
Firefox DevEdition only: Asynchronous Stacks in Console
Console stacks capture the full async execution flow for console.trace() and console.error(). This lets you understand scheduling of timers, events, promises, generators, etc. over time, which would otherwise be invisible.
They are only enabled in Firefox Developer Edition for now. We are working to make this feature available to all users after improving performance. Async stacks will also be rolled out to more types of logs, and of course the Debugger.
SignalR formatting & download/upload size for WebSockets
Before shipping the new WebSocket inspector in 71 we had it available in Firefox DevEdition and asked for your input. We didn’t just get a lot of fantastic ideas, some of you even stepped up to contribute code. Thanks a lot for that, and keep it coming!
Messages sent in ASP.NET’s Core SignalR format are now parsed to show nicely-formatted metadata. The bug was filed thanks to feedback from the ASP.NET community and then picked up by contributor Bryan Kok.
Similarly, the community asked to have the total transfer size for download and upload available. This is now a reality thanks to contributor Hayden Huang, who took up the bug as their first Firefox patch.
Start and end times for Network resources
The Timings tab of the Network Monitor now displays timings for each downloaded resource, making dependency analysis a lot easier:
- Queued — When the resource was queued for download.
- Started — When the resource started downloading.
- Downloaded — When the the resource finished downloading.
And as always, faster and more reliable
Here are just a few highlights from our continued performance and quality investments:
- In the Inspector, editing CSS is no longer blocked by CSP rules.
- The Inspector‘s badge for Custom Elements now correctly opens the original script for source maps.
- The Inspector now correctly preserves the selected element for
when reloading. - The Debugger now loads faster when many tabs are open, by prioritizing visible tabs first.
CSS additions
Now let’s move on to the most interesting new CSS features in Firefox 72.
Shadow Parts
One problem with styling elements contained inside a Shadow DOM is that you can’t just style them from CSS applied to the main document. To make this possible, we’ve implemented Shadow Parts, which allow shadow hosts to selectively expose chosen elements from their shadow tree to the outside page for styling purposes.
Shadow parts require two new features. The part attribute exposes an element inside a shadow tree to the outside page:
A paragraph
The ::part() pseudo-element is then used to select elements with a specific part attribute value:
custom-element::part(example) {
border: solid 1px black;
border-radius: 5px;
padding: 5px;
}CSS Motion Path
Motion Path is an interesting new spec for all you animators out there. The idea here is that you can define a path shape and then animate a DOM node along that path. The spec proposes an alternative to having to animate transform: translate(), position properties like top, right, and so on, or use some other property that often isn’t ideal and could result in very complex sets of keyframes.
With motion path, you define the shape of the path using offset-path:
offset-path: path('M20,20 C20,100 200,0 200,100');Define an animation to animate the element between different values of the offset-distance property, which defines how far along the defined path you want the element to appear:
@keyframes move {
0% {
offset-distance: 0%;
}
100% {
offset-distance: 100%;
}
}Then, animate the element using those keyframes:
animation: move 3000ms infinite alternate ease-in-out;This is a simple example. There are additional properties available, such as offset-rotate and offset-anchor. With offset-rotate, you can specify how much you want to rotate the element being animated. Use offset-anchor to specify which background-position of the animated element is anchored to the path.
Individual transform properties
In this release the following individual transform properties are enabled by default: scale, rotate, and translate. These can be used to set transforms on an element, like so:
scale: 2;
rotate: 90deg;
translate: 100px 200px;These can be used in place of:
transform: scale(2);
transform: rotate(90deg);
transform: translate(100px 200px);Or even:
transform: scale(2) rotate(90deg) translate(100px 200px);These properties are easier to write than the equivalent individual transforms, map better to typical user interface usage, and save you having to remember the exact order of multiple transform functions specified in the transform property.
JavaScript and WebAPI updates
If JavaScript is more your thing, this is the section for you. 72 has the following updates.
User gestures required for a number of permission-reliant methods
Notification permission prompts always show up in research as a top web annoyance, so we decided to do something about it. To improve security and avoid unwanted and annoying permission prompts, a number of methods have been changed so that they can only be called in response to a user gesture, such as a click event. These are Notification.requestPermission(), PushManager.subscribe(), and MediaDevices.getDisplayMedia().
By requiring a user gesture before the permission prompts are shown, Firefox significantly reduces permission spam, thereby strengthening users’ agency over their online experience.
So, for example, prompting for notification permission on initial page load is no longer possible. You now need something like this:
btn.addEventListener('click', function() {
Notification.requestPermission();
// Handle other notification permission stuff in here
});For more detail on associated coding best practices for Notification permissions, read Using the Notifications API.
Nullish coalescing operator
The nullish coalescing operator, ??, returns its right-hand side operand when its left-hand side operand is null or undefined. Otherwise, it returns its left-hand side operand.
This is a useful timesaver in a number of ways, and it is also useful when you only consider null and undefined to be unwanted values, and not other falsy values like 0 and ' '.
For example, if you want to check whether a value has been set and return a default value if not, you might do something like this:
let value;
if(!value) {
value = 'default';
}That’s a bit long, so you might instead use this common pattern:
let value;
let value = value || 'default';This also works OK, but will return unexpected results if you want to accept values of 0 or ' '.
With ??, you can do this instead, which is concise and solves the problem described above:
let value;
value = value ?? 'default';Event-based form participation
Event-based form participation is now enabled by default. This involves using the new FormData event, which fires when the form is submitted, but can also be triggered by the invocation of a FormData() constructor. This allows a FormData object to be quickly obtained in response to a formdata event firing, rather than needing to create it yourself — useful when you want to submit a form via XHR, for example.
Here’s a look at this feature in action:
formElem.addEventListener('submit', (e) => {
// on form submission, prevent default
e.preventDefault();
// construct a FormData object, which fires the formdata event
new FormData(formElem);
});
formElem.addEventListener('formdata', (e) => {
console.log('formdata fired');
// Get the form data from the event object
let data = e.formData;
// submit the data via XHR
let request = new XMLHttpRequest();
request.open("POST", "/formHandler");
request.send(data);
});Picture-in-picture for video now available on macOS & Linux
In the previous release post, we announced that Picture-in-picture had been enabled in Firefox 71, albeit this was for Windows only. However,today we have the goods that this very popular feature is now available on macOS and Linux too!
The post Firefox 72 — our first song of 2020 appeared first on Mozilla Hacks - the Web developer blog.
https://hacks.mozilla.org/2020/01/firefox-72-our-first-song-of-2020/
|
|
Will Kahn-Greene: Socorro Engineering: Year in Review 2019 |
Summary
Last year at about this time, I wrote a year in review blog post. Since I only worked on Socorro at the time, it was all about Socorro. In 2019, that changed, so this blog post covers the efforts of two people across a bunch of projects.
2019 was pretty crazy. We accomplished a lot, but picking up a bunch of new projects really threw a wrench in the wheel of ongoing work.
This year in review covers highlights, some numbers, and some things I took away.
Here's the list of projects we worked on over the year:
Crash stats: (aka Socorro) the Mozilla crash ingestion pipeline
Symbols server: (aka Tecken) the Mozilla symbols server
Buildhub and Buildhub2: indexes of builds of Mozilla products
PollBot and Delivery Dashboard: a system for showing release status
Mozilla Location Services: Mozilla's geolocation system
Read more… (13 min remaining to read)
|
|
Mozilla VR Blog: Mozilla Announces Deal to Bring Firefox Reality to Pico Devices |

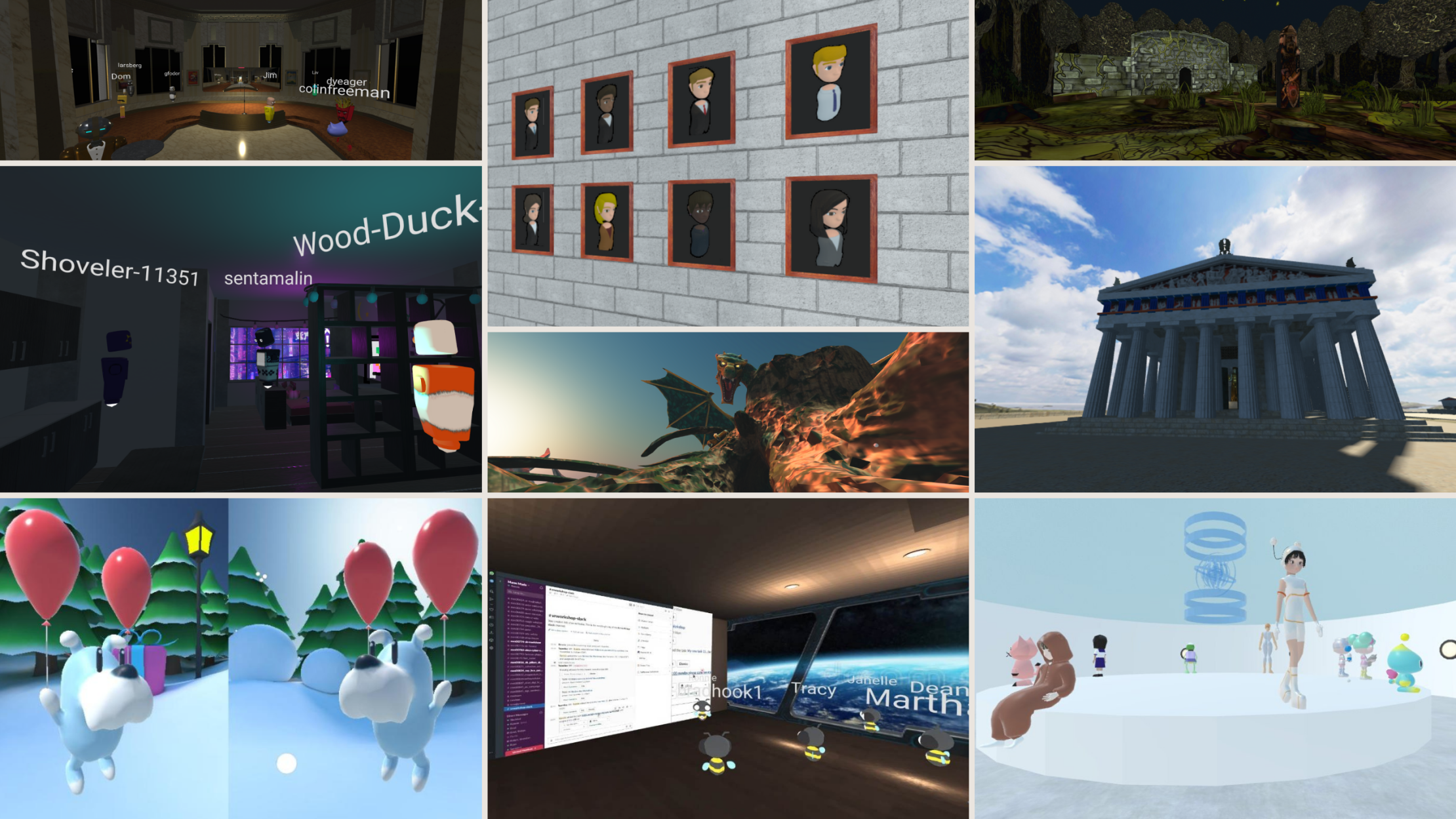
For more than a year, we at Mozilla have been working to build a browser that was made to showcase the best of what you love about browsing, but tailor made for Virtual Reality.
Now we are teaming up with Pico Interactive to bring Firefox Reality to its latest VR headset, the Neo 2 – an all-in-one (AIO) device with 6 degrees of freedom (DoF) head and controller tracking that delivers key VR solutions to businesses. Pico’s Neo 2 line includes two headsets: the Neo 2 Standard and the Neo 2 Eye featuring eye tracking and foveated rendering. Firefox Reality will also be released and shipped with previous Pico headset models.

This means anytime someone opens a Pico device, they’ll be greeted with the speed, privacy, and great features of Firefox Reality.
Firefox Reality includes the ability to sync your Firefox Account enabling you to send tabs, sync history and bookmarks, making great content easily discoverable. There’s also a curated section of top VR content, so there’s always something fresh to enjoy.
“We are pleased to be partnered with Pico to bring Firefox Reality to their users, especially the opportunity to reach more people through their large Enterprise audience,” says Andre Vrignaud, Head of Mixed Reality Platform Strategy at Mozilla. “We look forward to integrating Hubs by Mozilla to bring fully immersive collaboration to business.”
As part of Firefox Reality, we are also bringing Hubs by Mozilla to all Pico devices. In Hubs, users can easily collaborate online around virtual objects, spaces, and tasks - all without leaving the headset.
The virtual spaces created in Hubs can be used similarly to a private video conference room to meet up with your coworkers and share documents and photos, but with added support for all of your key 3D assets. You can fully brand the environment and avatars for your business, and with web-based access the meetings are just a link away, supported on any modern web browser.
Firefox Reality will be available on Pico VR headsets later in Q1, 2020. Stay tuned to our mixed reality blog and twitter account for more details.
https://blog.mozvr.com/mozilla-announces-deal-to-bring-firefox-reality-to-pico-devices/
|
|
Ryan Harter: Syncthing |
I did a lot of reading and exploring over my holiday break. One of the things I'm most excited about is finding Syncthing. If you haven't seen it yet, take a look. It's like and open-source decentralized Dropbox.
It works everywhere, which for me means Linux and Android. Google Drive …
|
|
Ryan Harter: Syncthing and Open Source Data Collection |
I don't see many open source packages collecting telemetry, so when Syncthing asked me to opt-in to telemetry I was intrigued.
I see a lot of similarities between how Syncthing and Firefox collects data. Both collect daily pings and make it easy to view the data you're submitting (in Firefox …
|
|
Cameron Kaiser: TenFourFox FPR18 available (and the classic MacOS hits Y2K20) |
Meanwhile, happy new year: classic Mac systems prior to Mac OS 9 are now hit by the Y2K20 bug, where you cannot manually use the Date and Time Control Panel to set the clock to years beyond 2019 (see also Apple Technote TN1049). This does not affect any version of MacOS 9 nor Classic on OS X, and even affected versions of the classic MacOS can still maintain the correct date until February 6, 2040 at 6:28:15 AM when the unsigned 32-bit date overflows. If you need to set the date on an older system or 68K Mac, you can either use a CDEV like Network Time, which lets you sync to a network time source or a local server if you have one configured (as I do), or you can use Rob Braun's SetDate, which allows you to manually enter a date or time through the entire supported range (and even supports System 6).
One other note is that all HFS+ volumes regardless of operating system version have the same year 2040 limit on dates -- that includes Intel Macs using HFS+ filesystems. You have 20 years to think about how you want to fix this (during which you should replace the PRAM batteries in your classic Macs, too).
http://tenfourfox.blogspot.com/2020/01/tenfourfox-fpr18-available-and-classic.html
|
|
Daniel Stenberg: Restored complete curl changelog |
For a long time, the curl changelog on the web site showed the history of changes in the curl project all the way back to curl 6.0. Released on September 13 1999. Older changes were not displayed.
The reason for this was always basically laziness. The page in its current form was initially created back in 2001 and then I just went back a little in history and filled up with a set of previous releases. Since we don’t have pre-1999 code in our git tree (because of a sloppy CVS import), everything before 1999 is a bit of manual procedure to extract so we left it like that.
Until now.
I decided to once and for all fix this oversight and make sure that we get a complete changelog from the first curl release all the way up until today. The first curl release was called 4.0 and was shipped on March 20, 1998.
Before 6.0 we weren’t doing very careful release notes and they were very chatty. I got the CHANGES file from the curl 6.0 tarball and converted them over to the style of the current changelog.
Notes on the restoration work
The versions noted as “beta” releases in the old changelog are not counted or mentioned as real releases.
For the released versions between 4.0 and 4.9 there are no release dates recorded, so I’ve “estimated” the release dates based on the knowledge that we did them fairly regularly and that they probably were rather spread out over that 200 day time span. They won’t be exact, but close enough.
Complete!
The complete changelog is now showing on the site, and in the process I realized that I have at some point made a mistake and miscounted the total number of curl releases. Off-by one actually. The official count now says that the next release will become the 188th.
As a bonus from this work, the “releaselog” page is now complete and shows details for all curl releases ever. (Also, note that we provide all that info in a CSV file too if you feel like playing with the data.)
There’s a little caveat on the updated vulnerability information there: when we note how far vulnerabilities go, we have made it a habit to sometimes mark the first vulnerable version as “6.0” if the bad code exists in the first ever git imported code – simply because going back further and checking isn’t easy and usually isn’t worth the effort because that old versions are not used anymore.
Therefore, we will not have accurate vulnerability information for versions before 6.0. The vulnerability table will only show versions back to 6.0 for that reason.
Many bug-fixes
With the complete data, we also get complete numbers. Since the birth of curl until version 7.67.0 we have fixed exactly 5,664 bugs shipped in releases, and there were exactly 7,901 days between the 4.0 the 7.67.0 releases.
https://daniel.haxx.se/blog/2020/01/04/restored-complete-curl-changelog/
|
|
Daniel Stenberg: curl receives 10K USD donation |
The largest ever single-shot monetary donation to the curl project just happened when indeed.com graciously boosted our economy with 10,000 USD. (It happened before the new year but as I was away then I haven’t had the chance to blog about it until now.)
curl remains a small project with no major financial backing, with no umbrella organization (*) and no major company sponsorships.
Indeed’s FOSS fund
At Indeed they run this awesome fund for donating to projects they use. See Duane O’Brien’s FOSDEM 2019 talk about it.
How to donate to curl
curl is not a legal, registered organization or company or anything that can actually hold on to assets such as money. In any country.
What we do have however, is a “collective” over at Open Collective. Skip over there to make monetary donations. Over there you also get a complete look into previous donations with full transparency as to what funds we have and spend in the project.
Money donated to us will only be spent on project related activities.
Other ways to donate to the project is of course to donate time and effort. Allow your employees to help out or spend your own time at writing code, fixing bugs or extend the documentation. Every little bit helps and will be appreciated!
curl sponsors
curl is held upright and pushing forward much thanks to the continuous financial support from champion companies. The primary curl sponsors being Haxx, wolfSSL, Fastly and Teamviewer.
The curl project’s use of donated money
We currently have two primary expenses in the project that aren’t already covered by sponsors:
The curl bug bounty. We’ve already discussed internally that we should try to raise the amounts we hand out as rewards for the flaws we get reported going forward. We started out carefully since we didn’t want to drain the funds immediately, but time has shown that we haven’t received so many reports and the funds are growing. This means we will raise the rewards levels to encourage researchers to dig deeper.
The annual curl up developers conference. I’d like us to sponsor top contributors’ and possibly student developers’ travels to enable a larger attendance – and a social development team dinner! The next curl up will take place in Berlin in May 2020.
(*) = curl has previously applied for membership in both Software Freedom Conservancy and Linux Foundation as they seemed like suitable stewards, but the first couldn’t accept us due to work load and the latter didn’t even bother to respond. It’s not a big bother, just reality.
https://daniel.haxx.se/blog/2020/01/03/curl-receives-10k-usd-donation/
|
|
About:Community: Firefox 72 new contributors |
With the release of Firefox 72, we are pleased to welcome the 36 developers who contributed their first code change to Firefox in this release, 28 of whom were brand new volunteers! Please join us in thanking each of these diligent and enthusiastic individuals, and take a look at their contributions:
- bayyatej.dev: 1576915
- ian_tong: 1592623
- jeff.lin.97: 1593919
- jeffinsam: 1592270, 1597700, 1597741, 1597881, 1597893, 1597979, 1598348, 1598528, 1598539, 1600476, 1600483, 1600484, 1600486
- u566121: 1247260
- xuelitan123: 1570477
- Alex J Garcia: 1565978, 1576672
- Anujan: 1590195
- Beatriz Rizental: 1365529
- Benjamin De Kosnik: 1580077
- Bert Peers: 1571971, 1571972, 1596769, 1596786, 1599644
- Bhopesh Bassi: 1391239
- Carson Greene: 1576911
- Dan Walsh: 1590358, 1597237
- Dorel Luca: 1581722
- Emily McDonough: 1588017, 1591925
- Erik Nordin: 1597642
- Hayden Huang: 1593831
- Jacob Stenson: 1591007, 1591989, 1592637, 1594082, 1597214
- James Hooks: 1585806
- James Jahns: 1576918, 1591474
- Jim Mason: 969322
- Kurt Miller: 1586912
- Kyle Kim: 1570502
- Lougenia Bailey: 1588948
- Philip J"agenstedt: 1589056
- Raymond Liu: 1214556
- Richard G: 1589333
- Rohit Awate: 1589072
- Sam Mauldin: 1592189
- Sid Vishnoi: 1575144, 1594306
- Subhamoy: 1595085, 1597959
- Taylor Southorn: 1371687, 1577073
- Thomas Kosmas: 1573781, 1590064
- Tony Wang: 1595256
- Travis Long: 1592315
- Vadim: 1592433
https://blog.mozilla.org/community/2020/01/02/firefox-72-new-contributors/
|
|
Mozilla Open Policy & Advocacy Blog: Bringing California’s privacy law to all Firefox users in 2020 |
2019 saw a spike of activity to protect online privacy as governments around the globe grappled with new revelations of data breaches and privacy violations. While much of the privacy action came from outside the U.S., such as the passage of Kenya’s data protection law and Europe’s enforcement of its GDPR privacy regulation, California represented a bright spot for American privacy.
Amidst gridlock in Congress over federal privacy rules, California marched forward with its landmark privacy law, the California Consumer Privacy Act (CCPA), which goes into effect on January 1, 2020. Mozilla has long been a supporter of data privacy laws that empower people — including CCPA. In fact, we were one of the few companies to endorse CCPA back in 2018 when it was before the California legislature.
The California Consumer Privacy Act (CCPA) expands the rights of Californians over their data – and provides avenues for the Attorney General to investigate and enforce those rights, as well as allowing Californians to sue. Californians now have the right to know what personal information is being collected, to access it, to update and correct it, to delete it, to know who their data is being shared with, and to opt-out of the sale of their data.
Much of what the CCPA requires companies to do moving forward is in line with how Firefox already operates and handles data. We’ve long believed that your data is not our data, and that privacy online is fundamental. Nonetheless, we are taking steps to go above and beyond what’s expected in CCPA.
Here’s how we are bringing CCPA to life for Firefox users.
CCPA rights for everyone.
When Europe passed its GDPR privacy law we made sure that all users, whether located in the EU or not, were afforded the same rights under the law. As a company that believes privacy is fundamental to the online experience, we felt that everyone should benefit from the rights laid out in GDPR. That is why our new settings and privacy notice applied to all of our users.
With the passage and implementation of CCPA, we will do the same. Changes we are making in the browser will apply to every Firefox user, not just those in California.
Deleting your data.
One of CCPA’s key new provisions is its expanded definition of “personal data” under CCPA. This expanded definition allows for users to request companies delete their user specific data.
As a rule, Firefox already collects very little of your data. In fact, most of what we receive is to help us improve the performance and security of Firefox. We call this telemetry data. This telemetry doesn’t tell us about the websites you visit or searches you do; we just know general information, like a Firefox user had a certain amount of tabs opened and how long their session was. We don’t collect telemetry in private browsing mode and we’ve always given people easy options to disable telemetry in Firefox. And because we’ve long believed that data should not be stored forever, we have strict limits on how long we keep telemetry data.
We’ve decided to go the extra mile and expand user deletion rights to include deleting this telemetry data stored in our systems. To date, the industry has not typically considered telemetry data “personal data” because it isn’t identifiable to a specific person, but we feel strongly that taking this step is the right one for people and the ecosystem.
In line with the work we’ve done this year to make privacy easier and more accessible to our users, the deletion control will be built into Firefox and will begin rolling out in the next version of the browser on January 7. This setting will provide users a way to request deletion for desktop telemetry directly from Firefox – and a way for us, at Mozilla, to perform that deletion.
For Firefox, privacy is not optional. We don’t think people should have to choose between the technology they love and their privacy. We think you should have both. That’s why we are taking these steps to bring additional protection to all our users under CCPA. And why we will continue to press in 2020 – through the products we build and the policies we advocate – for an Internet that gives people the privacy and security they deserve.
The post Bringing California’s privacy law to all Firefox users in 2020 appeared first on Open Policy & Advocacy.
|
|
Mozilla VR Blog: Happy New Year from Hubs! |
As we wrap up 2019, The Hubs team says thank you to the Mozilla Mixed Reality Community for an incredible year! We’ve been looking back and we’re excited about the key milestones that we’ve hit in our mission to make private social VR readily available to the general public. At the core of what we’re doing, our team is exploring the ways that spatial computing and shared environments can improve the ways that we connect and collaborate, and thanks to the feedback and participation of our users and community as a whole, we got to spend a lot of time this year working on new features and experiments.
Early in the year, we wanted to dive into our hypothesis that social 3D spaces could integrate into our existing platforms and tools that the team was regularly using. We launched the Hubs Discord Bot back in April, which bridged chat between the two platforms and added an optional authentication layer to restrict access to rooms created with the bot to users in a given server. Since launching the Discord bot, we’ve learned more about the behaviors and frameworks that enable healthy community development and management, and we released a series of new features that supported multiple moderators, configurable room permissions, closing rooms, and more.
One of our goals for this year was to empower users to more easily personalize their Hubs experiences by making it easy to create custom content. This work kicked off with making Spoke available as a hosted web application, so creators no longer had to download a separate application to build scenes for Hubs. We followed with new features that improved how avatars could be created, shared, remixed, and discovered, and we wrapped up the year by releasing several pre-configured asset kits for building unique environments, starting with the Spoke Architecture Kit release that also included a number of ease-of-use feature updates.
We’ve also just had a lot of fun connecting with users and growing our team and community, and we’ve learned a lot about what we’re working on and how to improve Hubs for different use cases. When we joined Twitter, we got to start interacting with a lot more of you on a regular basis and we’ve loved seeing how you’ve been using Hubs when you share your own content with us! The number of new scenes, avatars, and even public events that have been shared within our community gets us even more excited for what we think 2020 can bring.
As we look ahead into the next year, we’ll be sharing a big update in January and go in-depth with work we’ve been doing to make Hubs a more versatile platform. If you want to follow along with our roadmap, you can keep an eye on the work we have planned on GitHub and follow us on Twitter @ByHubs. Happy 2020!
|
|
The Firefox Frontier: New Year, New Rights: What to know about California’s new privacy law |
The California Consumer Privacy Act (CCPA) expands the rights of Californians over their data. Starting in 2020, Californians have the right to know what personal information is being collected, access … Read more
The post New Year, New Rights: What to know about California’s new privacy law appeared first on The Firefox Frontier.
|
|