How to make end-to-end encrypted calls in Facebook ... |
That in itself makes them less of a target for safety and security breaches. Cell Phones With the omnipresence of smart devices, calls over the cell phone network presently take up the biggest share of phone call volumes worldwide.
Since no cables are involved in making a cell phone call, anyone close by can in theory obstruct the signal. The overall security of a cell phone telephone call, though, depends on the stamina of these encryption protocols.
Despite the fact that these susceptabilities were dealt with when methods were updated, newer versions of encryption don't give complete safety either. A particular one - manipulating the SS7 method underlying virtually all mobile networks - only requires a hacker to understand your contact number. In 2019, cyberpunks utilized it to bypass a bank's text-based two-factor verification (2FA) to take from checking account - by obstructing texts as they were sent to customers' phones.
While text-based 2FA is a lot better than none, utilize a different method if you can. For delicate interaction, encrypted Vo, IP and carrier applications provide far better safety and security. Vo, IP Ultimately, Vo, IP is the contemporary gold requirement of call interaction - both via voice as well as video clip. Specifically during the pandemic, systems such as Zoom, Skype, and organization Vo, IP suppliers maintained the economic situation as well as private life going.
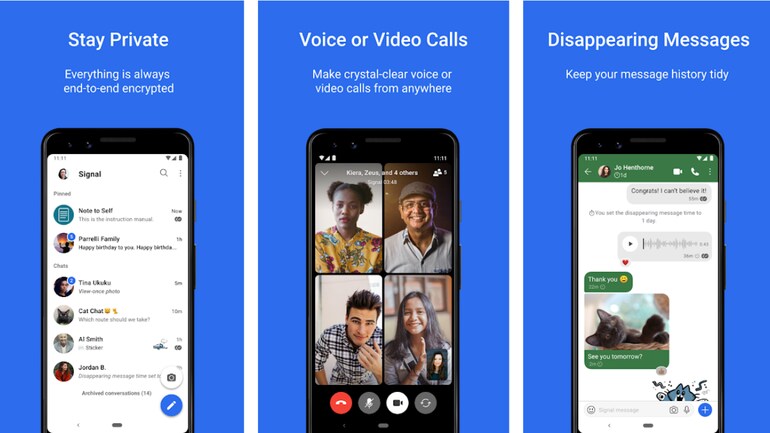
New Signal App Brings Encrypted Calling to iPhone - Threatpost
Unencrypted Vo, IP is as very easy to intercept as any various other web website traffic, for example using troubled Wi, Fi networks. At the current, this emerged during the ferocious argument around Zoom hacking. What's more, the safety and security risks in company Vo, IP systems are normally higher, considering that they also commonly integrate analytics platforms or customer connection administration (CRM) systems.
with superior end-to-end file encryption, utilizing only secure Wi, Fi networks - with Transportation Layer Protection (TLS) as well as Real-time Transport Protocol (SRTP) allowed - purchasing a VPN, and enabling 2FA make Vo, IP calls on par with those made via landlines in terms of security. The Bottom Line Different channels of interaction use different degrees of security for the details transferred.
Others, like Vo, IP, can provide maximum security just if service providers and also users stick to specific standards. In this electronic age, everyone requires to be knowledgeable about the threat of having personal or business details taken. Protect yourself by selecting the right channels, and also taking actions to make them as safe as feasible - to make sure that your delicate conversations stay risk-free from eavesdroppers.
What is end-to-end encryption? End-to-end encryption is a complicated term for a straightforward concept: that no one besides you as well as the person you're speaking with ought to be able to hear what you're saying over the phone. End-to-end file encryption has ended up being a market standard for real-time interactions such as messaging and also currently, we're bringing it to call, right from your Phone app.
Someone's listening: the real reasons you need to encrypt ...
With RingLeader CrowdVoice free international calling mobile app you can securely talk, message, meet, or hold a conference in one app? For only $15 per month, add three dedicated phone numbers in the US, Canada, or Mexico! Have a local presence from anywhere in the world. Sit on a beach in Spain and receive phone calls from your California office.
End-to-end file encryption is the latest addition to the collection of privacy and security functions that come included at no added cost in all Fi strategies, along with our integrated VPN for a private on the internet link and spam blocking to quit undesirable calls.
PHONE CALLS ENCRYPTION IN THE PASTThe art of securing remote conversations is rather old. Already throughout World War II, the initial security system called SIGSALY was developed.
SIGSALY videotaped audio waves at a rate of twenty thousand times per 2nd, writing them down in coded binary figures. Therefore, the transmission was basically indecipherable for the Germans that handled to intercept the signal. The audio released by SIGSALY appeared like the buzzing of a pest, which gave the devices code name - Environment-friendly Hornet.
File encryption of phone conversation was also made use of by e. g. Winston Churchill and Franklin Roosevelt. The success of the creation has triggered an eager passion in the modern technology of coding interaction at a distance. After completion of The second world war, the American safety and security system NSA (National Secure Company) developed a collection of STU I, STU II and also STU III encryption telephones.
Google Fi gets end-to-end encrypted phone calls - Big News ...
In 1989, the Irish firm Intrepid created a safe and secure phone called Milcode, providing security of phone call at fairly good degree. The encryption formulas were advanced and stood apart from previous competition versions. Milcode made use of key exchange modern technology with the Diffie-Hellman formula. The set of tricks traded between the recipient and the sender was created once again throughout each succeeding telephone call, which ensured a high level of call safety and security.
In the past, security telephones were made use of almost exclusively by the military, secret services and top-level political choice makers. The situation transformed with the enhancing appeal of mobile phones.
g. items to be provided, the business strategy for the coming months, new company companions and costs of the solutions supplied - these as well as far more data are possibly important target for a dishonest competitor. Eavesdropping as well as information theft is not only the domain of competitors in the expert area.
In truth this is not such a rare sensation. In 2017, the policemans got an authorization to develop 9725 wiretaps, which is why it is so important not to take too lightly the phenomenon and also to get file encryption telephones. This method is aimed mainly to deal with against organized criminal activity, lots of residents fear abuse of power in this location.
Mobile Phone Encryption Secure Encrypted Phone Calls and ...
 AECall , Encrypt Phone Call, Secure phone call - YouTube
AECall , Encrypt Phone Call, Secure phone call - YouTubeIn theory, calls made by the mobile phones ought to be secure - all information transferred by means of the GSM network is automatically secured with the A5 algorithm. Sadly, it is easy to recover cost when utilizing a lot less complicated programs than the abovementioned Pegasus. Thats why professional encryption telephones using techniques apart from common software application remedies appeared on the commercial market.
is a topic that has actually acquired fantastic popularity in recent years, likewise in Poland. Among the primary reasons for this is the expanding rate of interest in spy innovations - just in the very first quarter of 2016, sales of investigative devices and accessories (consisting of wiretaps) increased by 350% compared to in 2014.
 Secure Enterprise Communication Solutions
Secure Enterprise Communication Solutions  Encrypt your Mobile Phone Calls Easily with TrustCall
Encrypt your Mobile Phone Calls Easily with TrustCall THE VERY BEST ENCRYPTED PHONESThe offer of encryption phones is not very wide, at the very least when it involves the most reliable solutions. If you desire the most effective results, there is a choice in between the Enigma E2 as well as the most up to date service on the market - RAW Secure Phone and also RAW communicator.
The security phone makes use of an innovative two-step security process based on authentication and also discussion file encryption. Throughout authentication, a certification secured with the RSA algorithm is created. It is among the greatest security measures worldwide that makes it practically difficult to monitoring and intercept telephone calls despite having making use of the most modern-day tools and programs.
Google Fi receives end-to-end encrypted phone calls - First
To even more raise the level of security, the phone has no technology as well as applications that call for a long-term Web link - this stops any type of attempts of network monitoring. Despite the advanced services, Enigma E2 is easy to make use of and does not vary a lot from conventional cellphones in this respect.
The Enigma E2 encryption phone is a wonderful service that is very prominent over the years. Both products offer advanced remedies in the field of telephone call file encryption.
Customers just use one secure channel, each time receiving a various collection of secrets for subsequent telephone calls. The cryptographic component utilizes innovative primitives such as Curve25519, XSalsa20, Poly1305, Blake2 ensuring the greatest degree of security. Additionally, the communicator has a number of useful functionalities such as a personal address publication, text with the self-erasing system as well as a considerable BARK component that discovers all type of dangers to the os.
The application deals with mobile phones with the Android and also i, OS running systems. For that reason, it is a very versatile service that transforms your private or service phone right into a modern-day tool that enables you to secure call. In the beginning glance, the RAW Secure Phone encryption phone looks like a regular, modern smartphone.
TrustCall Secure Calling and Messaging - KoolSpan
It fits flawlessly in the hand of every entrepreneur. The most crucial capabilities of this phone are concealed from the eyes of outsiders - it ensures high safety thanks to the sophisticated system of security of telephone phone calls. Along with cheap international phone companies mounted, the file encryption phone has actually a modified os with its very own ROM.
An additional degree of defense is guaranteed by a cyber shield that protects the system versus 0-day attacks. The mix of the abilities of the RAW communicator and also modern technical services of the mobile phone cause the most effective tool available on the market, permitting the encryption of phone call.
Silent Phone is among numerous encrypted interaction solutions supplied by Quiet Circle, the programmer behind the Blackphone security-focused smart device array. Quiet Phone is a subscription-based service which utilizes end-to-end encryption with the keys held by the subscriber as opposed to the firm, and so no government eyes can snoop on your telephone calls.
Background Nasir is a journalist for Dundun Media. He has just got a lead on the location of a risk-free home utilized by AGA and he needs to call the Authorities. Point he does is to ensure his telephone call is secured. Right here's just how he did it. It's not truly a great time for protection as well as privacy.
Encrypted Communications - Dexter Edward LLC.
However that isn't stopping programmers from determining safe procedures as well as communication apps. is a brand-new, open-source Android and i, Phone application that promises secure calls. With Signal set up, you and also your close friend can call each other without your phone call being eavesdropped, snooped or figured out. Installing Signal Open the Google Play Shop on your Android gadget.
Faucet Install. When the installation surfaces, you'll discover the launcher for Signal on your home display or within your Application Drawer. Touch the icon to release the app.
Look for Signal. Download and install Signal. Faucet Install (encrypted phone calls). Review consent listing. If authorizations are appropriate, tap Accept. Enable setup to finish. Signal does not enable the taking of screenshots from within the application. Making use of Signal The first thing you need to do is confirm your device phone number. When triggered, see to it your phone number is proper and also faucet Register.
Once the number is validated, you will be prompted to use Signal as your default SMS app. Faucet Usage As Default SMS App and after that tap YES when motivated. (Keep in mind, you can still send out unencrypted texts, so it's fine to choose this app as your default SMS app.) You will after that be asked if you intend to import the system SMS messages; this will duplicate all of your phone's previous SMS messages into Signal's encrypted data source.
Google Fi Is Rolling Out End-To-End Encrypted Phone Calls ...
Discover the telephone call symbol and if you discover a padlock on the telephone call symbol, it just indicates the various other celebration has the signal app and also can do encrypted calls. See to publish comments and also obtain guidance from an area of security professionals.
Premium safety and security We protect trademark name business, international NGOs, federal government companies, as well as firms in such sectors as protection, power, and law. With Silent Phone, you're getting a costs product with first-class safety and security.
| Комментировать | « Пред. запись — К дневнику — След. запись » | Страницы: [1] [Новые] |






